I don’t know about soup trout, but goldfish are thriving.

I’m from space!
I don’t know about soup trout, but goldfish are thriving.



There are concepts of a plan
Me
Slashdot > Digg > Reddit > Lemmy
I don’t even take the packaging. I let the loose wet pickles roll around in my back seat.
Stupid sexy crack head


Have you and the other active mods considered adding a civility rule in the sidebar?
I still get panic attacks because they removed the polish sausage from the food court.


https://www.apple.com/customer-letter/answers/
Quote below
No.
We regularly receive law enforcement requests for information about our customers and their Apple devices. In fact, we have a dedicated team that responds to these requests 24/7. We also provide guidelines on our website for law enforcement agencies so they know exactly what we are able to access and what legal authority we need to see before we can help them.
For devices running the iPhone operating systems prior to iOS 8 and under a lawful court order, we have extracted data from an iPhone.
We’ve built progressively stronger protections into our products with each new software release, including passcode-based data encryption, because cyberattacks have only become more frequent and more sophisticated. As a result of these stronger protections that require data encryption, we are no longer able to use the data extraction process on an iPhone running iOS 8 or later.
Hackers and cybercriminals are always looking for new ways to defeat our security, which is why we keep making it stronger.


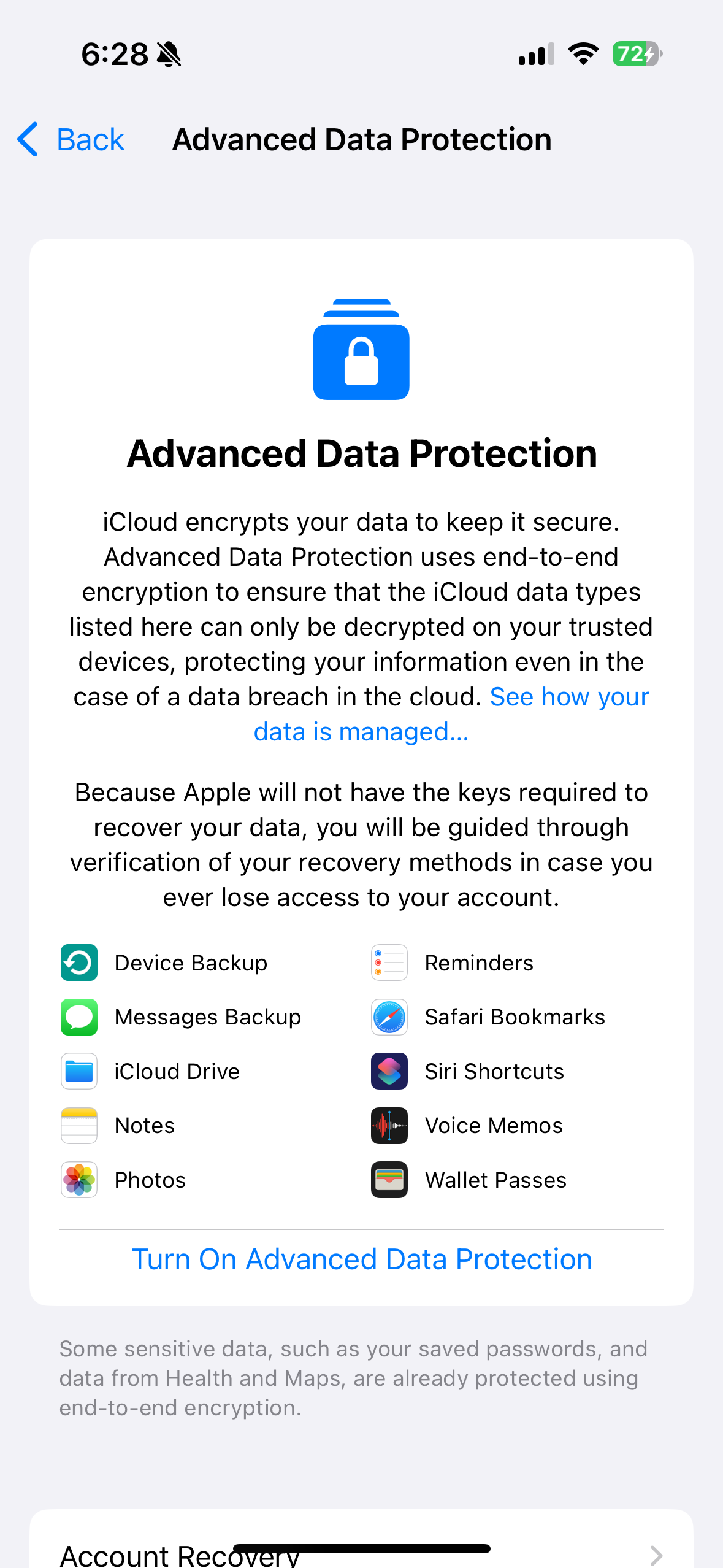
This is for non e2ee cloud data. If you turn e2ee cloud encryption on, only you can access your cloud data. A government or police agency can’t access it, but you’re also kind of fucked if you need Apple’s support to access backup. So maybe leave it off for old parents.


That is key is not for locally encrypted data, locked devices or e2ee data.
https://support.apple.com/en-gb/guide/security/sec973254c5f/web
If you turn this on, Apple can’t not decrypt anything you have stored in the cloud with that key.


Do you have a source for that?
Because Apple has had a lot of very prominent court cases about unlocking phones for cops, and they famously haven’t done that. They, like other cloud service providers, have forked over cloud storage data, that isn’t e2ee, when given a warrant.


They’ll hand over unencrypted cloud data, but they are not decrypting E2EE cloud data. They literally can’t. They don’t have the key. If they had a key, it would be a monumental security vulnerability.
This is why governments and cops have dragging them into courts for years.


Scouting locations for surveillance pidgins and presidential weather control stations.


Once you get 3/4 through this article, and get to the actual content, it’s pretty underwhelming. Apple was basically just showing cops that they could be querying their existing databases with iOS mobile and or CarPlay experiences.


After reading the article, it doesn’t look like any of this contradicts what they’re been selling. Encrypted data is still locked down. IMHO, this title is fairly clickbaity.
A lot of this looks like iOS / CarPlay versions of policing / public records database software that was previously on platforms like Windows.


This title seems kind of clickbaity. Most of the native apps are for querying existing government and police databases. We’re talking about accessing records via CarPlay, as opposed to using a bulky Window’s laptop docked in a center console.
Apple is still not offering governments a backdoor into encrypted content.
Alternative theory. Reverse image search is imperfect.