I was setting up my laptop for traveling and adding Wireguard VPN configuration.
The Wireguard config generated by router only contains IPv4 address (10.0.5.x), and while testing the VPN to my surprise “what is my ip” websites can find my IPv6 address (I USB tethered mobile connection to my laptop).
It looks like NetworkManager does nothing about IPv6 connection if VPN doesn’t have IPv6 settings, which is bad for road warrior type of VPN configuration.
Is there an easy toggle to turn of IPv6 if VPN is connected and otherwise? Or is only option to disable all IPv6 no matter what?
I’d also like to know, is there a way to just turn off this ipv6 trashfire? Preferably in a universal, cross-distro way?
Seems like the most universal way is: GRUB_CMDLINE_LINUX_DEFAULT=“ipv6.disable=1”
In my case just disable IPv6 in WiFi is enough.
sysctl looks like the most universal way.
net.ipv6.conf.all.disable_ipv6 = 1
net.ipv6.conf.default.disable_ipv6 = 1Or you could just… learn to use the modern internet that 60% of internet traffic uses? Not everyone has a dedicated IPv4 anymore, we are in the days of mobile networks and CGNAT. IPv4 exhaustion is here today.
Idk why my comment was removed. I just said most internet traffic is chinese bots which are not sentient so they’re okay with using IPv6 instead of IPv4 like people do.
IPv4 exhaustion is ofc a problem. But IPv6 discarding NAT is like throwing the baby out with the bathwater.
Yikes. By most internet traffic you mean Chinese bots yeah?
Yeah I’ll stay behind my one NAT instead of six godzillion firewalls thanks.
Or you could just… learn to use the modern internet that 60% of internet traffic uses? Not everyone has a dedicated IPv4 anymore, we are in the days of mobile networks and CGNAT. IPv4 exhaustion is here today.
Where are you getting 60%? Google’s IPv6 Adoption page has it under 50% still:
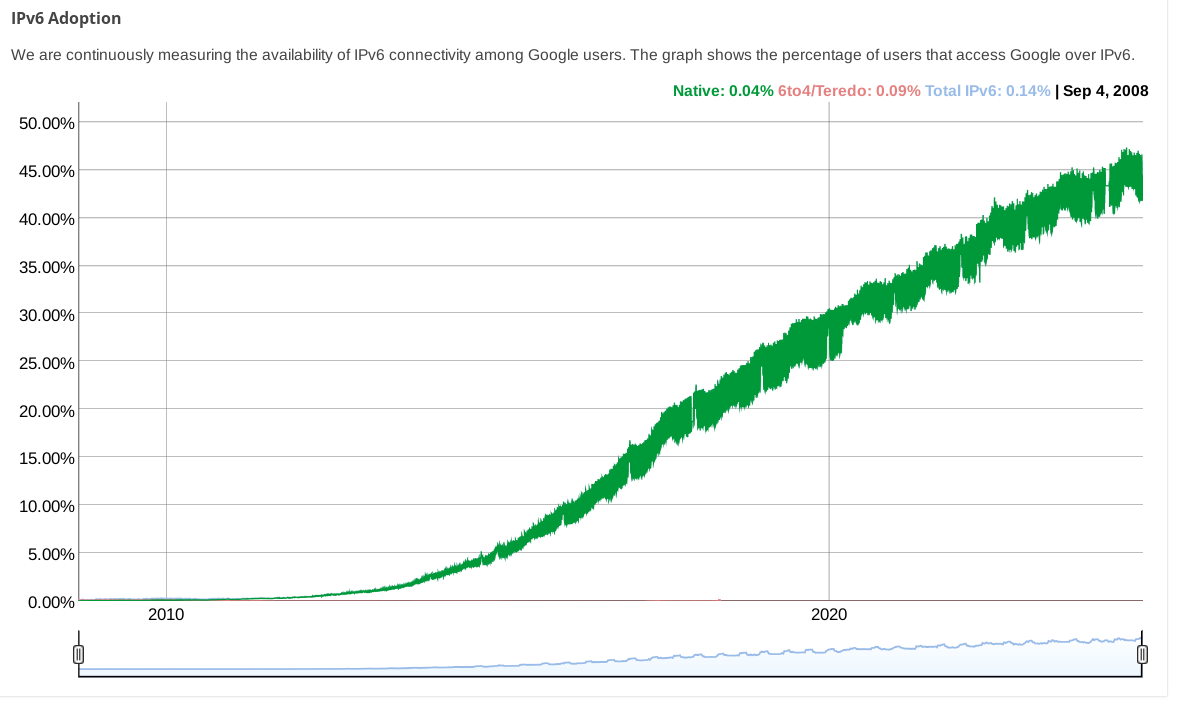
(while other stats pages from big CDNs show even less)
Huh, I misremembered then. I stand corrected.
Notable though that there are specific countries (such as India) where adoption is far higher at 72%
I keep hoping someone will come up with a half-measure that looks like ipv4 with an extra octet and writable in hex.
- Let people stew a bit on their 00c0a8011f IP which is like a 192.168.1.31 IP.
- increment the big number. Oh shit, we’ve got lots.
- repeat
- start adding the cool parts of ipv6
- moar
- add a 00 to the end that old shit just skips
- somewhere in there, switch the engine
We can either take yeeeears to do it well, or we can take more decades to try and big-bang it. This ain’t 1983.
Hmm, how about we have public facing IPv6 to gateway and then NAT to IPv4 internally. I wouldn’t have a problem with it then. In general I wouldn’t even have a problem with IPv6 or v8 or whatever even internally as long as we’ll always have NAT.
ipv4 with an extra octet
that was proposed as “IPv4.1” on April 1, 2011: https://web.archive.org/web/20110404094446/http://packetlife.net/blog/2011/apr/1/alternative-ipv6-works/
You could edit your configuration to change the wireguard connection’s
AllowedIPsfrom0.0.0.0/0to0.0.0.0/0,::/0so that IPv6 traffic is routed over it. Regardless of if your wireguard endpoint actually supports it, this will at least stop IPv6 traffic from leaking.Wireguard config already includes “::/0”
I tried the same setup with Ubuntu 24.04.1 desktop live system and I can replicate this IP leak issue, I guess I will have to disable IPv6.
Disable in network manager?
That is what I was thinking, yes.
Best to set a firewall rule with nftables to block non-vpn traffic from leaving (you should also do the save for IPv4 traffic to prevent leaks in case the tunnel disconnects)


